There are three broad categories of files in Linux.
- General Files – These are ordinary files made up of binary or ASCII data. These are regular files such as documents, images, audio and video files, etc.
- Directory Files – In Linux, directories are also categorized as files since they also serve as storage space for other files and folders.
- Device Files – These are special files that provide an interface to device drivers which enable the usability of hardware devices on the system such as mice, keyboards, USB devices, hard drives, etc. These are found in the /dev directory.
Linux Directory Structure Diagram
A standard Linux distribution follows the directory structure as provided below with Diagram and explanation.
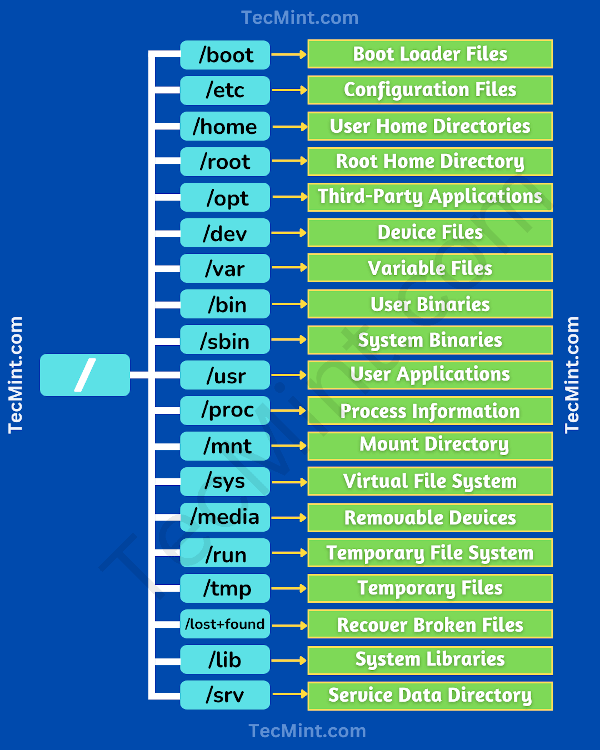
Each of the above directories (which is a file, in the first place) contains important information, required for booting to device drivers, configuration files, etc. Describing briefly the purpose of each directory, we are starting hierarchically.
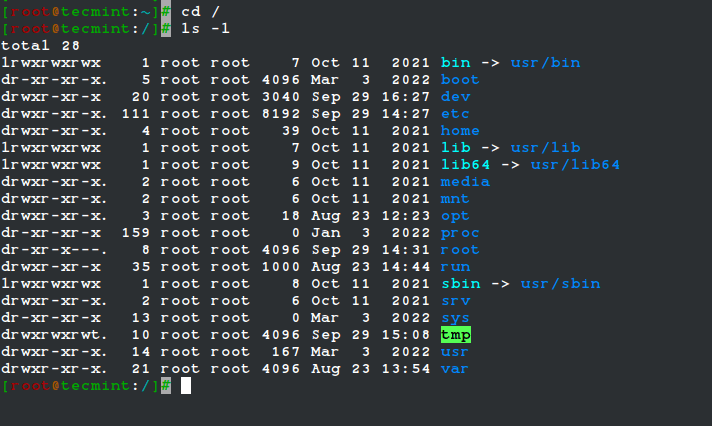
/ Directory
The root directory, denoted by a single forward slash (/), is the uppermost directory in the Linux directory structure. It contains all directories, sub-directories, and files on your Linux system. It’s from the root directory where the Linux directory hierarchy starts.
NOTE: The root directory (/) should not be confused with the root home directory (/root).
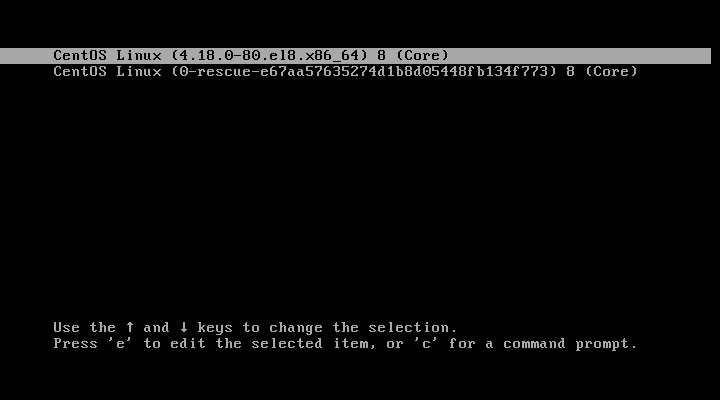
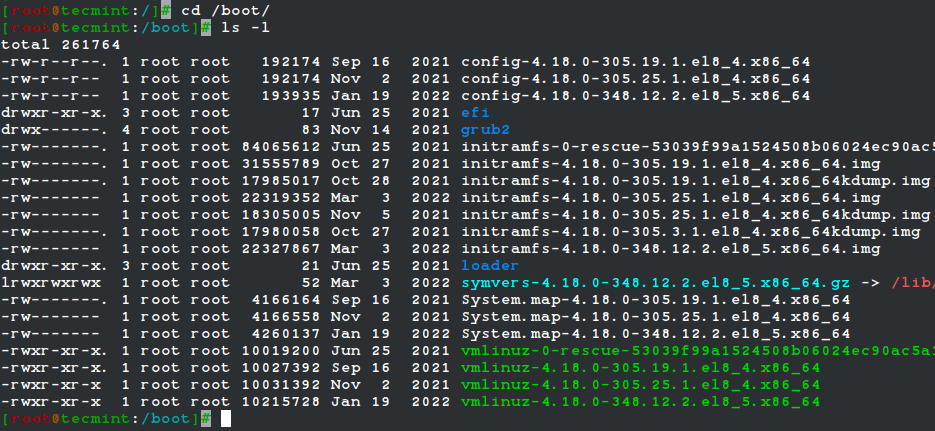
/boot Directory
This is one of the most vital directories in a Linux system. As the name infers, the boot directory contains Linux boot files such as the bootloader, the kernel, and its associated files. Files such as ‘vmlinuz‘ represent the compressed image of the Linux kernel.
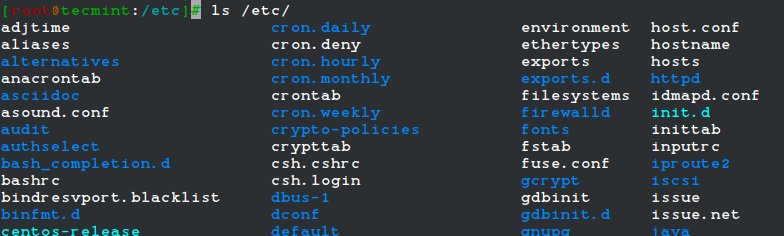
/etc Directory
The /etc directory contains system configuration files for all the services, scripts, and third-party applications that are installed. This directory is considered the nerve center of the Linux system.
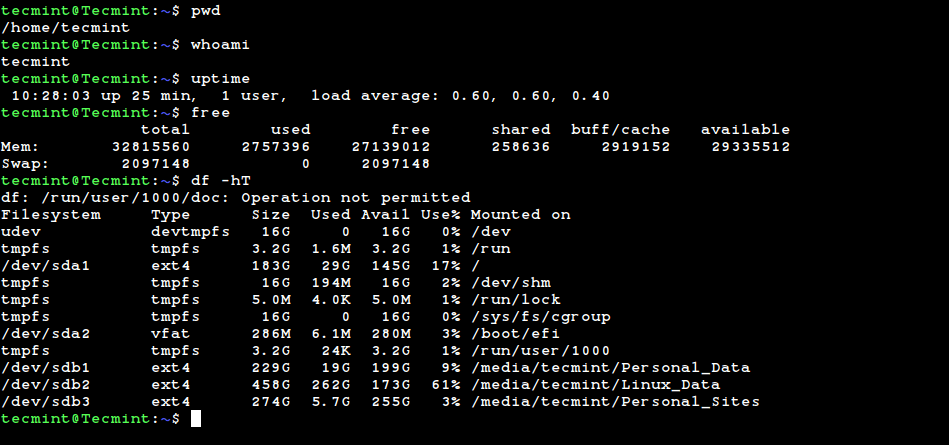
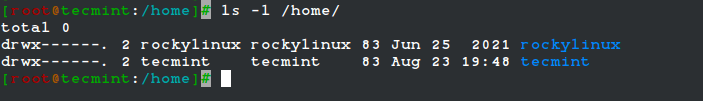
/home Directory
The /home directory is a directory that contains a user’s personal folders and files. On a graphical Linux system, the home directory, by default, contains folders such as Desktop, Documents, Downloads, Pictures, Videos, and Public.
In addition, the /home directory contains personal configuration files which are prefixed with a dot (.). These are hidden files that contain user-specific settings for the login shell session.
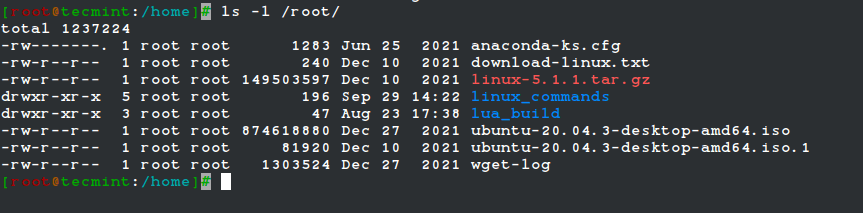
/root Directory
The /root directory is the home directory for the root user, which is also referred to as the root user’s home directory (and not as the root (/) directory).
The root account also referred to as the superuser, administrative user, system administrator or just the root user has all the access to commands and system files in Linux.
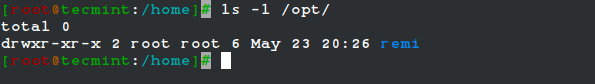
/opt Directory
The /opt directory is a directory that is reserved for add-on packages and third-party software applications that are not included by default in the system’s official repositories.
For example, when you install applications such as Skype, Discord, Spotify, and Java, to mention a few, they get stored in the /opt directory.
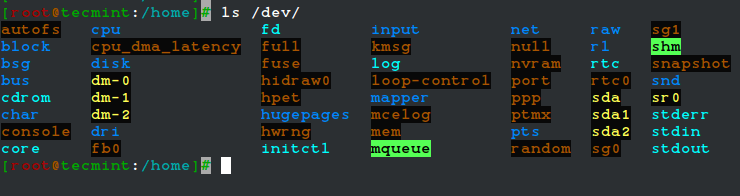
/dev Directory
The /dev directory contains device files or special files for devices that are attached to the system such as the hard drive, keyboard, and mouse. As mentioned, these are not regular that a user can read and write to.
These are abstractions of standard devices that applications on your system interact with through input and output system calls.
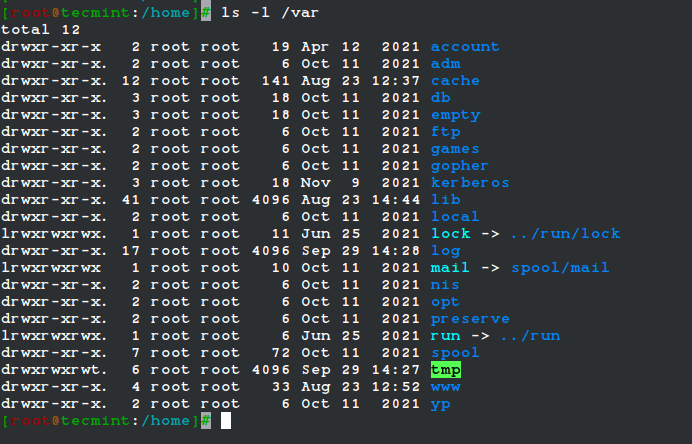
/var Directory
The /var directory stores system-generated variable files, which include log files, caches, and spool files just to mention a few.
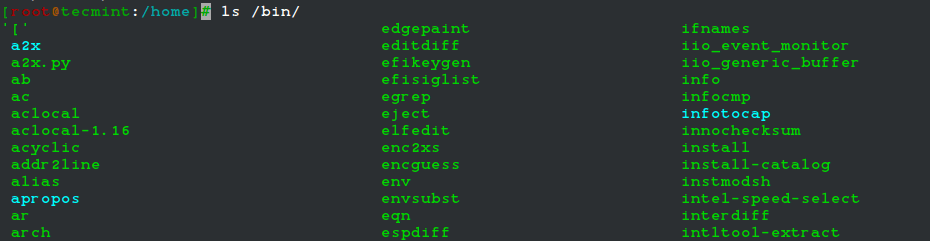
/bin Directory
The /bin directory contains user binaries, executable programs, and common system commands that are used by all users in the system. These include ls, pwd, cat, mkdir, cd, mv, cp, du, df, tar, rpm, wc, history, etc.
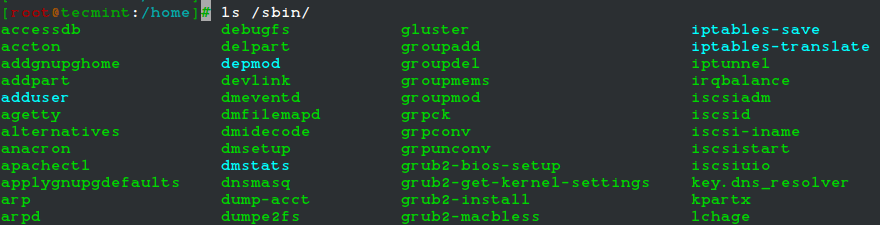
/sbin Directory
The /sbin directory contains executable files, utilities, and system commands that are reserved for the root user or a user with root privileges. Such commands include halt, reboot, mkfs, fsck, fdisk, halt, iptables, ifconfig, ip, swapon, etc.
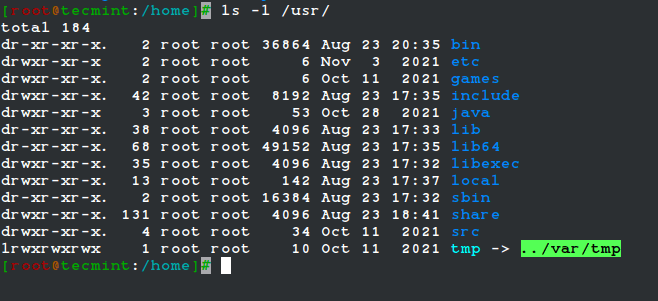
/usr Directory
The /usr directory ranks as one of the most important directories due to the enormous amount of data it holds. The directory contains system-wide read-only files. These include libraries, user binaries and their documentation, programs, and system utilities.
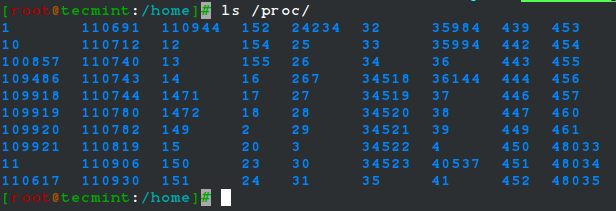
/proc Directory
The /proc directory is somewhat of a strange directory. It is a virtual or pseudo filesystem that contains vital information about running processes. It is considered the control and information center for the Linux kernel.
The filesystem is created on the fly upon system startup and is destroyed once the system is powered off.
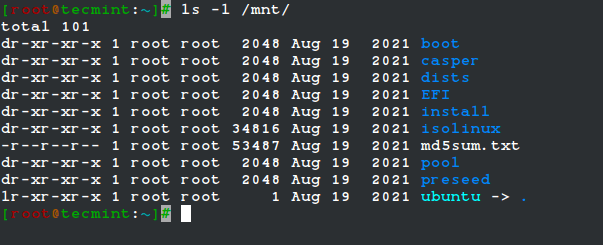
/mnt Directory
The /mnt directory along with its subdirectories is a directory intended to be used as a temporary mount point for mounting storage devices such as Hard disk drives, USB drives, and CDROMs.
/sys Directory
The /sys is a virtual file system that contains a set of virtual files that provide an interface to the Linux kernel.
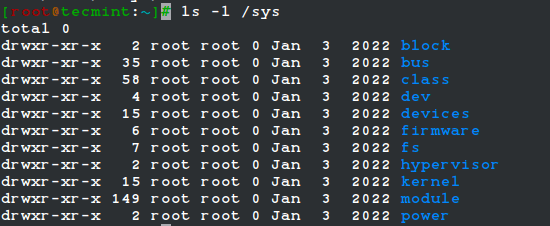
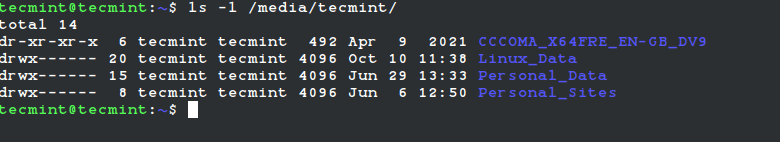
/media Directory
The /media directory is a directory where the system mounts removable media such as USB drives.
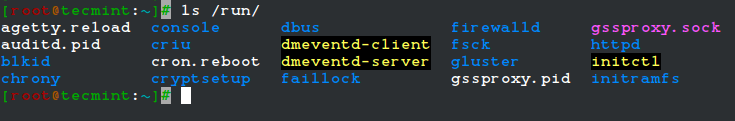
/run Directory
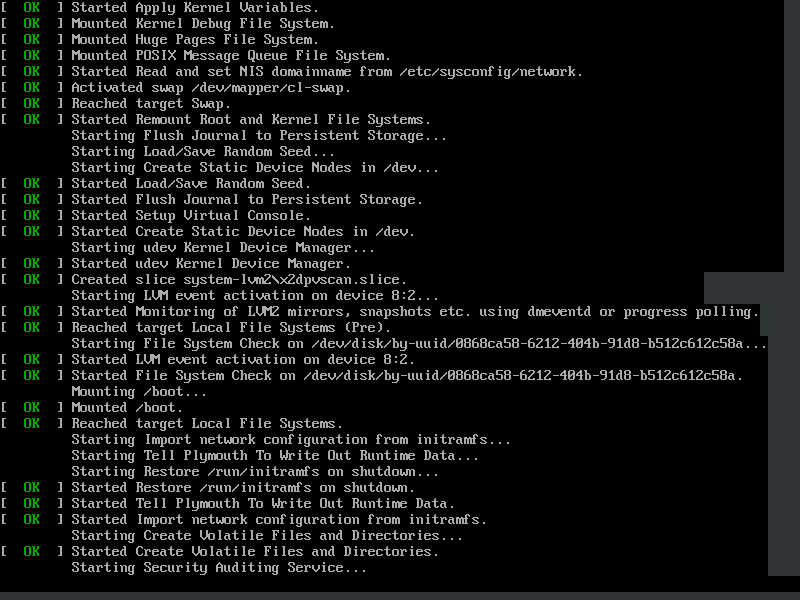
The /run directory is a temporary filesystem that contains volatile runtime data that shows the system has since it was booted. Files under the /run directory must be deleted (removed or truncated as convenient) at the start of the boot process.
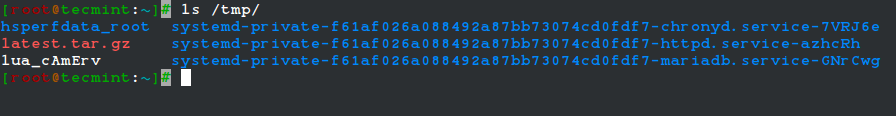
/tmp Directory
The /tmp directory is a directory that stores temporary files and many programs use this directory to create lock files and keep the temporary storage of data.
Do not delete files under the/tmp directory unless you know exactly what you are doing! Many of these files are critical for presently running programs and removing them may affect a system crash.
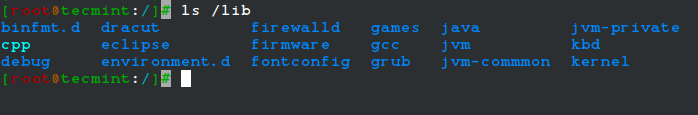
/lib Directory
The /lib directory stores all the essential standard libraries required by user binaries in the /bin directory.
/lost+found Directory
The lost+found directory is installed during the installation of Linux, useful for recovering files that may be broken due to unexpected shut-down.
/srv Directory
The /srv directory is the service directory and is abbreviated as ‘srv‘. This directory contains server-specific and service-related files.
Exploring Important file, their location, and their Usability
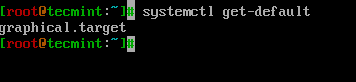
Linux is a complex system that requires a more complex and efficient way to start, stop, maintain and reboot a system, unlike Windows. There is a well-defined configuration file, binaries, man pages, info files, etc. for every process in Linux.
In addition to the major directories, here is a list of some of the prominent files and directories and their uses.
- /boot/vmlinuz : The Linux Kernel file.
- /dev/hda : Device file for the first IDE HDD (Hard Disk Drive).
- /dev/hdc : Device file for the IDE Cdrom, commonly.
- /dev/sda: Device file for the first SATA Drive (Hard Disk Drive).
- /dev/null : A pseudo-device, that doesn’t exist. Sometimes garbage output is redirected to /dev/null, so that it gets lost, forever.
- /etc/bashrc : This file contains system-wide defaults, functions, and aliases among other files that are used by all the system users.
- /etc/crontab : This is a system-wide file that is uniquely formatted to schedule or automate system tasks on a Linux system.
- /etc/exports : A file that determines which file systems are exported to remote hosts and specifies options.
- /etc/fstab : This is a special file that contains information about all avaiable mount points and mount point options. Each line in this file provides six options, each of which denotes information about a mount point or filesystem.
- /etc/hosts : This is a configuration file that maps system hostnames to their corresponding IP addresses.
- /etc/hosts.allow : The file specifies which hosts are permitted to connect to the local system.
- /etc/host.deny : The file specifies which hosts are denied access and services on the local machine.
- /etc/issue : Contains a pre-login message.
- /etc/modules : This file contains the names of kernel modules that should be loaded at boot time, one per line.
- /etc/motd : motd stands for a message of the day, the message users get upon login.
- /etc/mtab : A read-only file that contains a list of currently mounted filesystems.
- /etc/passwd : A file that contains the system user’s information such as the username, UID, GID, and login shell among others
- /etc/printcap : Contains printer information that is generated by the /etc/cups/printers.conf file.
- /etc/profile : Contains Linux system-wide environment and other startup scripts.
- /etc/profile.d : Application script, executed after login.
- /etc/rc.d : Information about run level specific script.
- /etc/rc.d/init.d : Run Level Initialisation Script.
- /etc/resolv.conf : This is a DNS resolver file. It specifies how the system leverages DNS to resolve hostnames.
- /etc/security : Contains configuration files for various PAM modules.
- /etc/skel : This is a directory that contains a set of user configuration files that are copied to the user’s home directory when a user is created.
- /etc/X11 : This is a directory that contains configuration files for the X-window System.
- /usr/bin : Normal user executable commands.
- /usr/bin/X11 : This directory contains infinitely nested directories and binaries for the X Windows System.
- /usr/include : The directory contains header files for C compilers. This includes stdio.h, stdlib.h, and string.h among others.
- /usr/share : Shared directories of man files, info files, etc.
- /usr/lib : This directory consists of object files and directories
- /usr/sbin : The directory contains binaries with superuser privileges or for System Administration.
- /proc/cpuinfo : The file contains system info including CPU model, model name, number of cores, and clock speed to mention a few files.
- /proc/interrupts : Information about the current interrupts being utilized currently.
- /proc/ioports : The file contains all the Input/Output addresses used by devices on the server.
- /proc/meminfo : A file that stores memory usage information including swap information.
- /proc/modules : A file that lists all the modules being used by the kernel
- /proc/mount : The file contains detailed mounted file-system information.
- /proc/stat : The file contains detailed information about the system and kernel activity.
- /proc/swaps : The file contains information about the swap file.
- /proc/version : The file contains Linux version information.
- /var/log/lastlog : A binary file that contains information about the last successful user logins.
- /var/log/messages : The file contains a log of messages produced by the syslog daemon at boot.
- /var/log/syslog : A file that contains non-critical system logs.
- /var/log/wtmp : A file listing the login time and duration of each user on the system currently.