Introduction
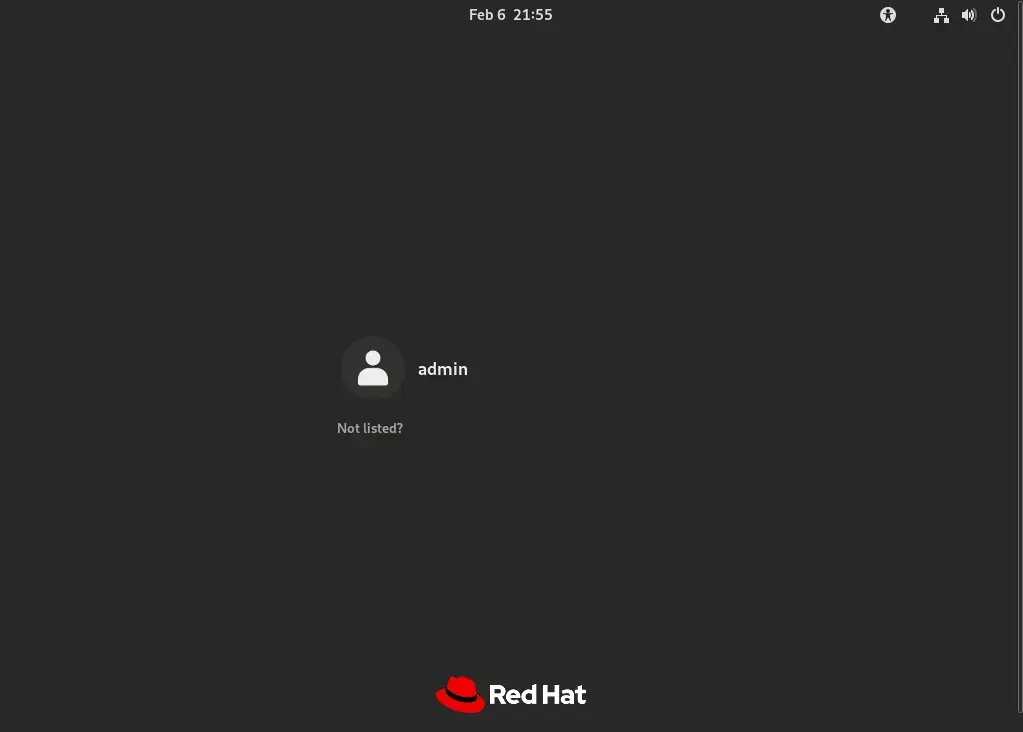
In the expansive realm of operating systems, the sheer variety of options can often leave users bewildered. Yet, amidst this sea of choices, Red Hat and Kali Linux emerge as prominent figures, each with its own dedicated following and specific niche. Red Hat, epitomized by its flagship offering, Red Hat Enterprise Linux (RHEL), excels in serving the needs of enterprise environments, providing unmatched stability, security, and scalability.
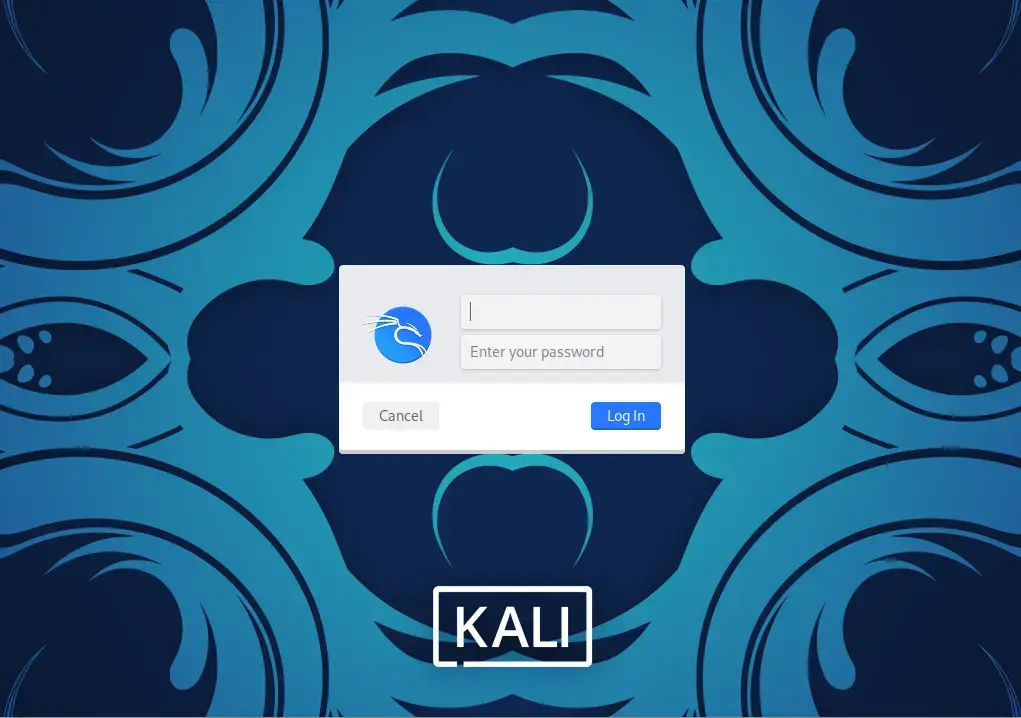
Conversely, Kali Linux, a powerhouse in the domain of cybersecurity, offers a comprehensive toolkit tailored for security professionals and ethical hackers. With its vast array of pre-installed security tools and a focus on cutting-edge penetration testing capabilities, Kali Linux has become indispensable for those navigating the complex landscape of digital security. Thus, while both Red Hat and Kali Linux share a foundation in the Linux ecosystem, their divergent focuses and distinct feature sets make them indispensable choices for users with disparate needs and objectives.
10 Major Differences Between Red Hat and Kali Linux
Now let’s take a close look at 10 of the major differences between these two operating systems, shedding light on their unique characteristics, functionalities, and target audiences.
Purpose and Target Audience
|
|
Default Package Selection
|
|
Release Cycle and Support
|
|
User Interface
|
|
Documentation and Support Resources
|
|
Default Security Policies
|
|
Package Management
|
|
Licensing
|
|
Customization and Flexibility
|
|
Legal and Ethical Considerations
|
|

No comments:
Post a Comment